App Information of Magisk Manager
| App Name | Magisk Manager vv8.0.0 |
|---|---|
| Genre | Android APP |
| Size | 3.1 MB |
| Latest Version | v8.0.0 |
| Get it On |  |
| Update | Oct 03, 2020 |
| Package Name | MagiskManager-v8.0.0.apk |
| Rating | 4.7 ( 4126 ) |
| Installs | 16894 |
Description of Magisk Manager
Magisk Manager v8.0.0 apk download on this page.
If you need stub-release.apk file Download here.
This version change log details Add v21.0 release notes.
**** details.md ****
Internal Details
File Structure
Paths in “Magisk tmpfs directory”
Magisk will mount a `tmpfs` directory to store some temporary data. For devices with the `/sbin` folder, it will be chosen as it will also act as an overlay to inject binaries into `PATH`. From Android 11 onwards, the `/sbin` folder might not exist, so Magisk will randomly create a folder under `/dev` and use it as the base folder.
“`
# In order to get the current base folder Magisk is using,
# use the command `magisk –path`.
# Binaries like magisk, magiskinit, and all symlinks to
# applets are directly stored in this path. This means when
# this is /sbin, these binaries will be directly in PATH.
MAGISKPATH=$(magisk –path)
# Magisk internal stuffs
MAGISKTMP=$MAGISKBASE/.magisk
# Magisk’s BusyBox directory. Within this folder stores
# the busybox binary and symlinks to all of its applets.
# Any usage of this directory is deprecated, please
# directly call /data/adb/magisk/busybox and use
# BusyBox’s ASH Standalone mode.
# The creation of this path will be removed in the future.
$MAGISKTMP/busybox
# /data/adb/modules will be bind mounted here.
# The original folder is not used due to nosuid mount flag.
$MAGISKTMP/modules
# The current Magisk installation config
$MAGISKTMP/config
# Partition mirrors
# Each directory in this path will be mounted with the
# partition of its directory name.
# e.g. system, system_ext, vendor, data …
$MAGISKTMP/mirror
# Block devices Magisk creates internally to mount mirrors.
$MAGISKTMP/block
# Root directory patch files
# On system-as-root devices, / is not writable.
# All pre-init patched files are stored here and bind mounted.
$MAGISKTMP/rootdir
“`
Paths in `/data`
Some binaries and files should be stored on non-volatile storages in `/data`. In order to prevent detection, everything has to be stored somewhere safe and undetectable in `/data`. The folder `/data/adb` was chosen because of the following advantages:
– It is an existing folder on modern Android, so it cannot be used as an indication of the existence of Magisk.
– The permission of the folder is by default `700`, owner as `root`, so non-root processes are unable to enter, read, write the folder in any possible way.
– The folder is labeled with secontext `u:object_r:adb_data_file:s0`, and very few processes have the permission to do any interaction with that secontext.
– The folder is located in *Device encrypted storage*, so it is accessible as soon as data is properly mounted in FBE (File-Based Encryption) devices.
“`
SECURE_DIR=/data/adb
# Folder storing general post-fs-data scripts
$SECURE_DIR/post-fs-data.d
# Folder storing general late_start service scripts
$SECURE_DIR/service.d
# Magisk modules
$SECURE_DIR/modules
# Magisk modules that are pending for upgrade
# Module files are not safe to be modified when mounted
# Modules installed in Magisk Manager will be stored here
# and will be merged into $SECURE_DIR/modules in the next reboot
$SECURE_DIR/modules_update
# Database storing settings and root permissions
MAGISKDB=$SECURE_DIR/magisk.db
# All magisk related binaries, including busybox,
# scripts, and magisk binaries. Used in supporting
# module installation, addon.d, Magisk Manager etc.
DATABIN=$SECURE_DIR/magisk
“`
Magisk Booting Process
Pre-Init
`magiskinit` will replace `init` as the first program to run.
– Early mount required partitions. On legacy system-as-root devices, we switch root to system; on 2SI devices, we patch fstab and execute the original `init` to mount partitions for us.
– Load sepolicy either from `/sepolicy`, precompiled sepolicy in vendor, or compile split sepolicy
– Patch sepolicy rules and dump to `/sepolicy` or `/sbin/.se` or `/dev/.se`
– Patch `init` or `libselinux.so` to force the system to load the patched policies
– Inject magisk services into `init.rc`
– Execute the original `init` to continue the boot process
post-fs-data
This triggers on `post-fs-data` when `/data` is decrypted and mounted. The daemon `magiskd` will be launched, post-fs-data scripts are executed, and module files are magic mounted.
late_start
Later in the booting process, the class `late_start` will be triggered, and Magisk “service” mode will be started. In this mode, service scripts are executed.
Resetprop
Usually, system properties are designed to only be updated by `init` and read-only to non-root processes. With root you can change properties by sending requests to `property_service` (hosted by `init`) using commands such as `setprop`, but changing read-only props (props that start with `ro.` like `ro.build.product`) and deleting properties are still prohibited.
`resetprop` is implemented by distilling out the source code related to system properties from AOSP and patched to allow direct modification to property area, or `prop_area`, bypassing the need to go through `property_service`. Since we are bypassing `property_service`, there are a few caveats:
– `on property:foo=bar` actions registered in `*.rc` scripts will not be triggered if property changes does not go through `property_service`. The default set property behavior of `resetprop` matches `setprop`, which **WILL** trigger events (implemented by first deleting the property then set it via `property_service`). There is a flag `-n` to disable it if you need this special behavior.
– persist properties (props that starts with `persist.`, like `persist.sys.usb.config`) are stored in both `prop_area` and `/data/property`. By default, deleting props will **NOT** remove it from persistent storage, meaning the property will be restored after the next reboot; reading props will **NOT** read from persistent storage, as this is the behavior of `getprop`. With the flag `-p`, deleting props will remove the prop in **BOTH** `prop_area` and `/data/property`, and reading props will be read from **BOTH** `prop_area` and persistent storage.
Magic Mount
The details of the actual implementation and algorithm of Magic Mount is omitted here, please directly dive into the source code if interested (`core/module.cpp`).
Even though the mounting logic is very complicated, the final result of Magic Mount is actually pretty simple. For each module, the folder `$MODPATH/system` will be recursively merged into the real `/system`; that is: existing files in the real system will be replaced by the one in modules’ system, and new files in modules’ system will be added to the real system.
There is one additional trick you can use: if you place an empty file named `.replace` in any of the folders in a module’s system, instead of merging the contents, that folder will directly replace the one in the real system. This will be very handy in some cases, for example swapping out a system app.
If you want to replace files in `/vendor` or `/product`, please place them under `$MODPATH/system/vendor` or `$MODPATH/system/product`. Magisk will transparently handle both cases, whether vendor or product is a separate partition or not.
SELinux Policies
Magisk will patch the stock `sepolicy` to make sure root and Magisk operations can be done in a safe and secure way. The new domain `magisk` is effectively permissive, which is what `magiskd` and all root shell will run in. `magisk_file` is a new file type that is setup to be allowed to be accessed by every domain (unrestricted file context).
Before Android 8.0, all allowed su client domains are allowed to directly connect to `magiskd` and establish connection with the daemon to get a remote root shell. Magisk also have to relax some `ioctl` operations so root shells can function properly.
After Android 8.0, to reduce relaxation of rules in Android’s sandbox, a new SELinux model is deployed. The `magisk` binary is labelled with `magisk_exec` file type, and processes running as allowed su client domains executing the `magisk` binary (this includes the `su` command) will transit to `magisk_client` by using a `type_transition` rule. Rules strictly restrict that only `magisk` domain processes are allowed to attribute files to `magisk_exec`. Direct connection to sockets of `magiskd` are not allowed; the only way to access the daemon is through a `magisk_client` process. These changes allow us to keep the sandbox intact, and keep Magisk specific rules separated from the rest of the policies.
The full set of rules can be found in `magiskpolicy/rules.cpp`.
Content
- What is Android Rooting?
- What Magisk Manager?
- History of magisk manager apk
- Why you should do a Magisk download?
- How to Download Magisk Latest Version For Android 2021
- Magisk Manager installation on Android - External method
- Magisk Manager installation on Android - Custom Recovery option
- Uninstalling Magisk manager apk download
- FAQs
- Is rooting the android devices legal?
- Is Magisk Manager Risk-Free?
- Can Magisk Manager download for free?
- Does Magisk compatible with my android version?
- Why is Magisk won't function well on my phone?
What is Android Rooting?
It simply means unlocking the android operating system to grant access to the unauthorized section of the phone. Even though you own the handset, you don't have full authority over the phone. You just log in to the system as a user. But after you root it, you can do whatever you want with your device. Such as installing apps that unapproved, unlock the bootloader and remove unwanted bloatware, installing custom ROMs, and customize it furthermore as you wish.
It's kind of similar to apple jailbreak. And the most amazing part is android rooting can also be led to high performance and longer battery life. Well, now you know about rooting. Then what is the connection between android rooting and the Magisk Manager? Hang on, we are going to talk about it.
What Magisk Manager?
As they say it, it's a mask for android. Does that complicate things for you even more? well, if you are new to android rooting you probably have no idea that there are some struggles that have to be overcome when you have a rooted device. If you have a rooted android phone, you don't get OTA updates! Yeah, that's right. You have to unroot it, then get the update and root again. And some applications won't even allow running in rooted handsets. Especially banking applications.
That's when the Magisk manager apk comes to the rescue. It's a systemless rooting solution. It can cover the rooted system like a mask and you won't have to be bothered to go between rooting and unrooting. It doesn't affect the core code either. You can get OTA updates, use banking applications and do whatever you couldn't do from a rooted mobile phone.
History of magisk manager apk
Topjohnwu was a developer in the android developer team. He was the one who launched the Magisk Manager in 2016 as the best solution that can go through the android safety net. And since the first release to the latest Magisk apk version 23.0, he has been developing it adding convenient features, and upgrading it. So now we can go for Magisk manager apk download which has much more convenient characteristics than then.
Why you should do a Magisk download?
There are a bunch of new characteristics that come with Magisk latest version 23.0.0. According to the Magisk manager GitHub page, we can expect more in the future because the developer planning to add more improvements in the future as well.
- Magisk Manager apk can download to any regular android phone and then you can root it.
- It allows you to go through google safety net.
- It let you add and modify files. Furthermore, since it is open source you can make changes to default coding and make it work for you as you want.
- The mount feature is really convenient. It allows you to change the core and partition levels as well. Moreover, you can make changes to all the system and media files and store them as you prefer in memory.
- Read-only files including prop files can be changed from the Resetprop feature.
- You can build and include your own repositories in the application.
- You can download any app from any site without the approval of the android OS.
How to Download Magisk Latest Version For Android 2021
Now the design and implementation are much convenient in Magisk than earlier you don't have to download separate files for Magisk zip and Magisk manager apk. There is only one app now.
But before you do the Magisk manager apk download there are some things that you should take care of.
- It's convenient to learn some of the basics in ADB and fastboot.
- The device bootloader should be unlocked before installing the Magisk zip.
- You have to flash custom ROM once again to use stock boot.img. But only if you are using the boot.img mods.
- Custom kernel installation is necessary.
Magisk Manager installation on Android - External method
1. First go Magisk manager apk download for the mobile phone.
2. Enable the unknown sources to turn on un settings and then install the downloaded Magisk app
3. Now install it once more by clicking on the "install" button on the message you will see.
4. Actually that's all. Now you have installed it.
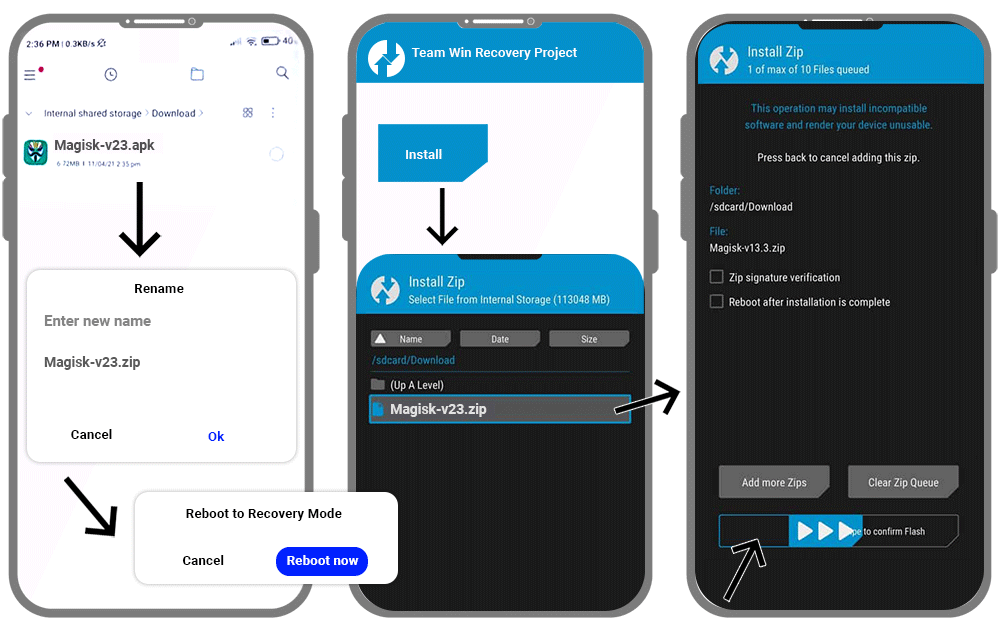
Magisk Manager installation on Android - Custom Recovery option
TWRP is a custom recovery solution for Android mobile phones. After you install this tool, you can back up the system and download thrid party firmware as well. Therefore make sure to back the system before starting to proceed.
- First, install TWRP on your android phone.
- Then you have to download Magisk Manager APK
- Now you have to rename the extension to .apk for the .zip. (Magisk zip)
- Reboot your device into TWRP recovery mode.
- Now click the install button on the TWRP recovery boot menu
- Then go to internal storage -->Magisk.zip --> Select storage
- Next, install the zip file
- When it completes the installation open the file -->Reboot system
- If it works you have installed Magisk Manager successfully.
Uninstalling Magisk manager apk download
Method 1 - Using the App
- Magisk app icon -->Uninstall --> An alert message --> Complete Uninstall
- Next, the app asks for permission to activate the uninstaller file. -->Click allow
- Then the Magisk uninstaller will be downloaded and uninstall the installed Magisk APK.
- Finally, it will be reboot automatically.
Method 2 - Using TWRP Recovery
- First, you should have the Magisk app on your phone.
- Next, rename its extension to uninstall.zip.
- Then switch off the mobile phone and boot it into the recovery mode.
- Now click the install button on the recovery menu and select the Magisk Uninstaller zip file.
- Slide the slider then and the installation will be started.
- Finally, reboot the device and Magisk will be removed once you check it.
FAQs
Is rooting the android devices legal?
In short, Yes. But it is legal as long as you root your android smartphone. Because many manufacturers allow it nowadays. However, rooting android tablets are illegal.
Is Magisk Manager Risk-Free?
Since there are many users but never get complaints about malware, viruses, or any spam, we can assure you Magisk is a pretty good and safe rooting solution. Furthermore, it won't modify boot partitions or the system partitions. And neither install third-party applications without your consent.
Can Magisk Manager download for free?
Absolutely. It offers the facilities to download, install and manage the device completely free of charge.
Does Magisk compatible with my android version?
It's compatible with all the android versions above 4.1 and 4.2 And your compressed boot image on an android mobile phone should be gzip compressed boot.img.
Why is Magisk won't function well on my phone?
If you have installed the application externally, that might be the reason for this issue. Therefore it's better if you uninstall that and install Magisk apk to your device's internal storage.